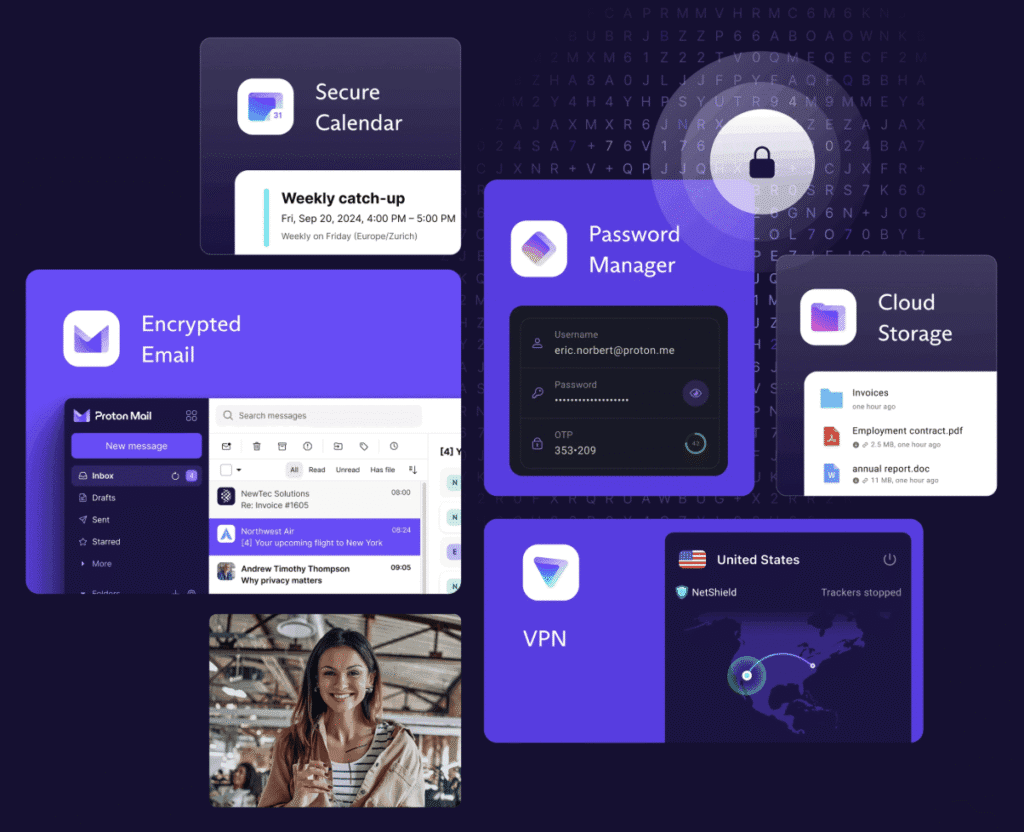
Yes! Devices like AirTags or Tiles use Bluetooth Low Energy (BLE) for proximity tracking (~10-50m range), while rogue hotspots spoof WiFi signals for man-in-the-middle attacks or location fingerprinting. Our de-googled Privacy Phones counter these with kernel-level blocks and pre-loaded tools – far beyond stock Android/iOS which often lack native defences.
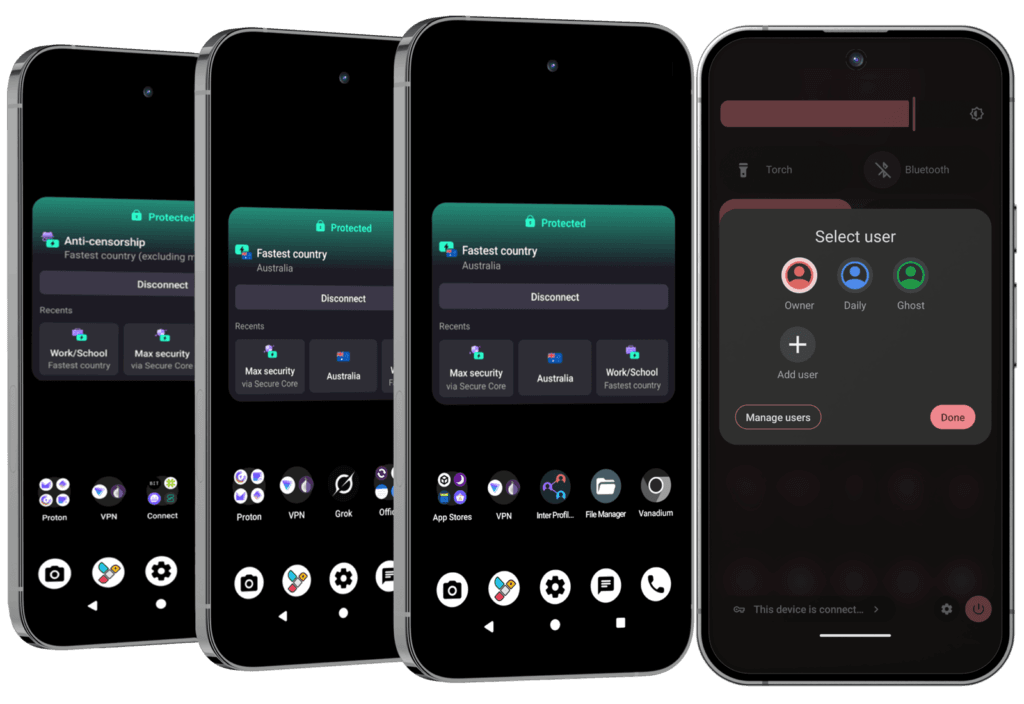
Our ‘Pro Bundle‘ Privacy Phones integrate advanced scanning in its ‘Ghost’ profile for privacy threats like stalking or surveillance:
- Geofencing: Apps create BLE-based virtual fences (~50m radius) and can push alerts if trackers enter/exit zones (e.g., home/car perimeter during protests or travel). Customisable for family/activism; tamper-proof with low false alarms.
- BLE Scanning/Blocking: Detects trackers (AirTags, Tiles, Find My) via background scans; auto-alerts, plays sounds to locate, blocks signals; logs history for patterns. Real scenario: Ping if a stalker’s tag follows you – false positives minimised via filters.
- WiFi Signal Analysis: Spot rogue hotspots by revealing hidden SSIDs, signal strengths, and anomalies (e.g., duplicate networks); evades fingerprinting via channel optimisation.
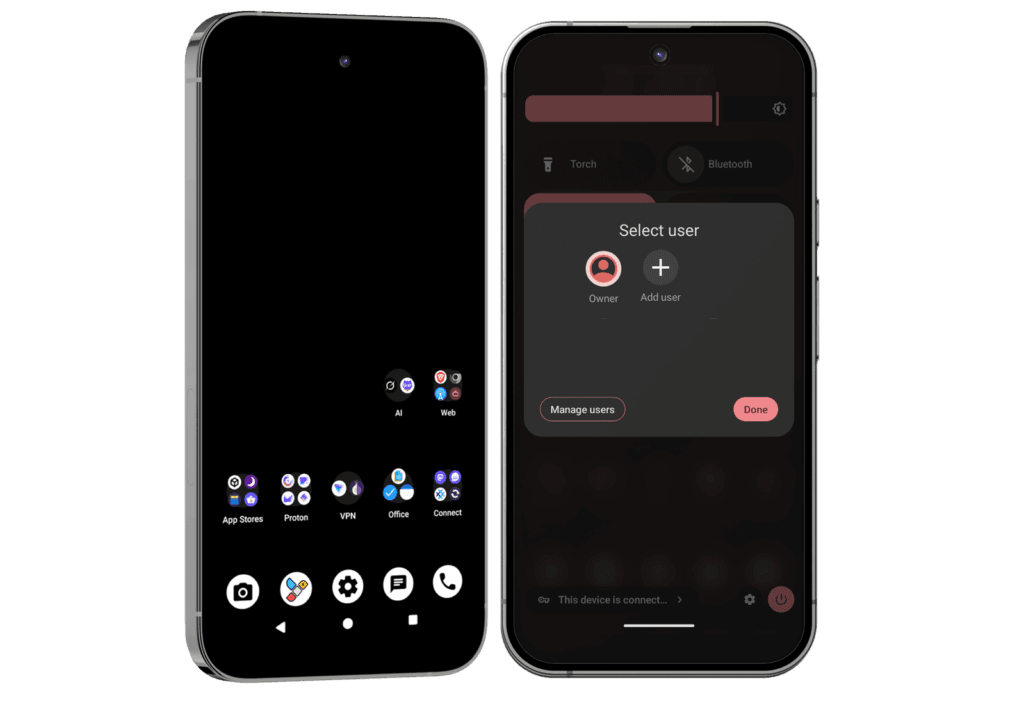
- Full Integration: One-tap kills in Quick Settings (Bluetooth/WiFi/sensors); pairs with per-connection MAC randomisation, network toggle (blocks localhost), and Proton VPN for layered anonymity.
- Off-Grid Extras (Pro Bundle): Verified Boot tamper alerts; Faraday bag blocks all radio signals; signal logs for forensics – ideal for high-risk scenarios.
If you know… you know. Shop our Privacy Phones now!