In today’s hyper-connected world, your phone knows more about you than your family and closest friends. From tracking your location to monitoring your searches and conversations, standard Android or iOS devices from big tech giants turn your personal data into goldmine. But what if you could break free?
Switching to a Privacy Phone in 2026 isn’t just a tech upgrade – it’s a powerful move towards protecting your personal information, enhancing your security, and enjoying peace of mind. At PrivacyPros, Australia’s best provider of de-googled privacy phones, we make this switch simple, secure, and accessible for everyone – even if you’re not a tech expert.
Whether you’re a busy professional handling sensitive data, a parent wanting to keep kids safe online, a traveller avoiding unwanted tracking, a vulnerable individual evading threats, or just someone tired of constant ads and surveillance – a privacy phone gives you back control.
With the rise of AI, making the switch could be one of the best decisions you make this year.
Rising Need for Privacy Phones
Digital privacy isn’t a luxury; it’s necessity. With new laws around age verification, online surveillance, and data breaches – Australians are waking up to the risks of everyday smartphones. Traditional phones collect your data silently – location history, app usage, contacts, device sensors, and even voice patterns – to fuel advertising, profiling or worse.
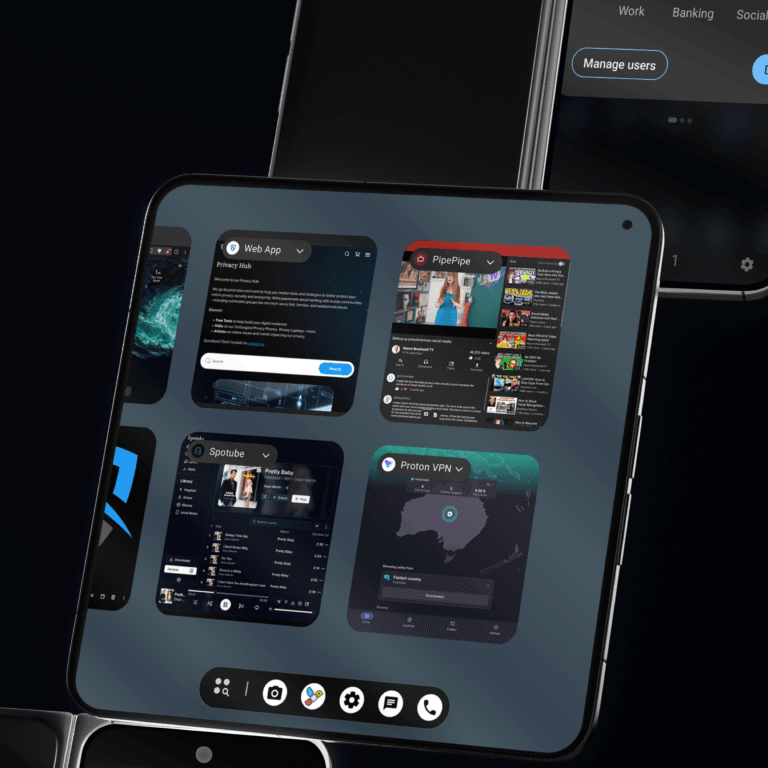
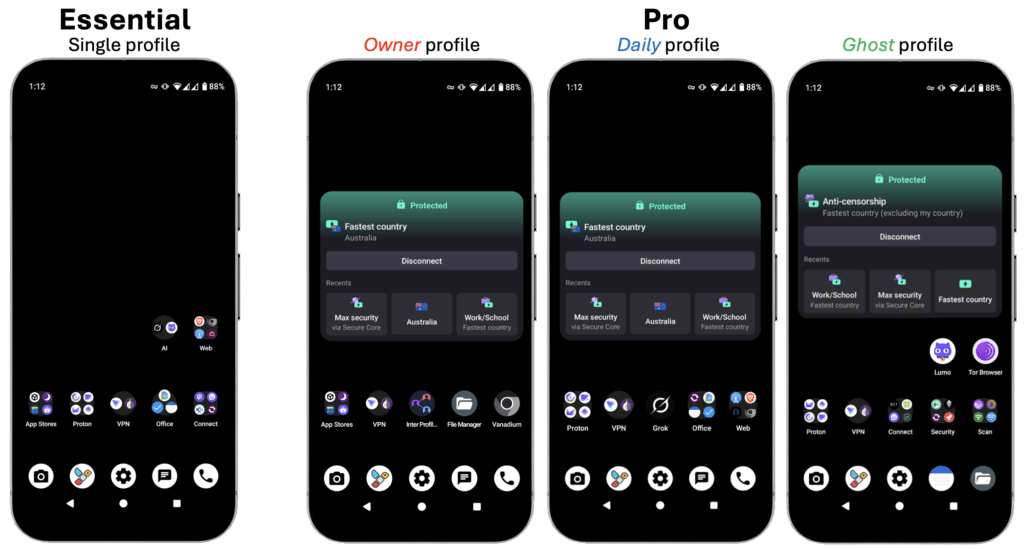
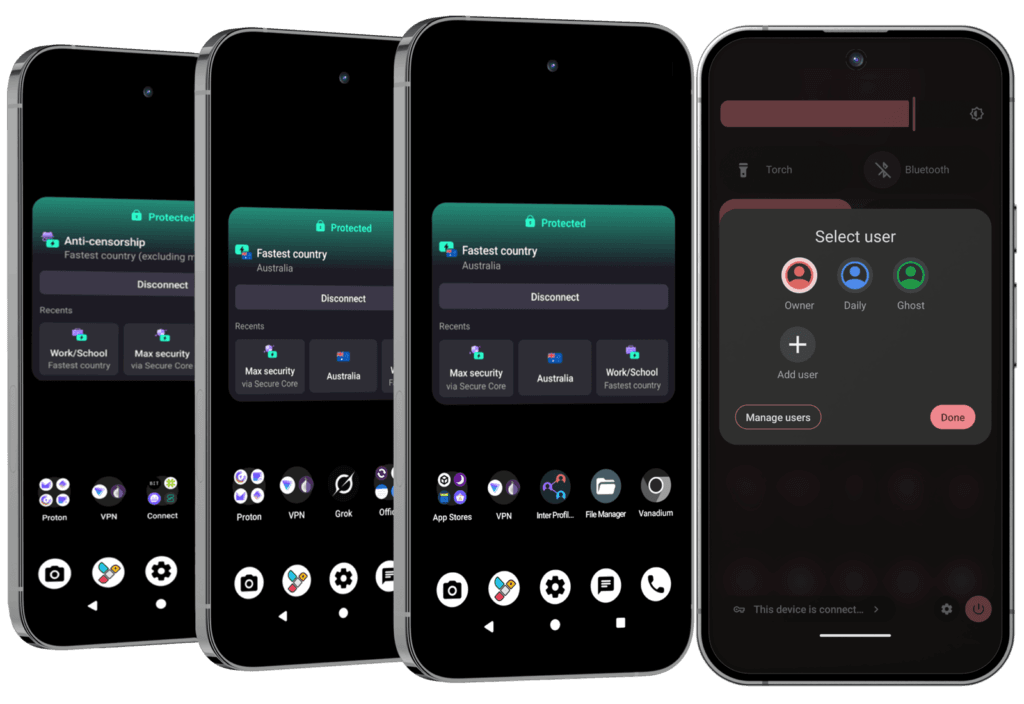
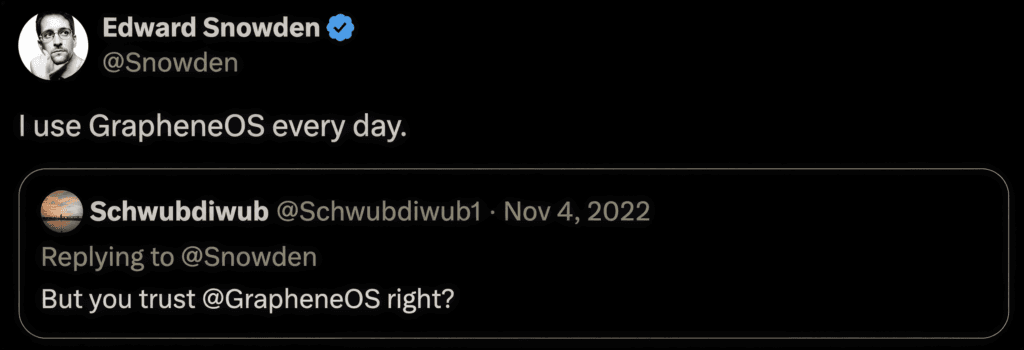
A privacy phone, like our de-googled Pixel devices running GrapheneOS (a highly secure operating system endorsed by privacy experts like Edward Snowden), flips the script. It removes Big Tech’s built-in trackers, giving you a clean, secure device without compromising on functionality. No more mandatory Google or Apple accounts tied to your identity.
Key Benefits
Here’s why so many Aussies are making the switch:
- Ultimate Data Protection: Your personal info stays yours. No background data harvesting means less risk of identity theft, targeted scams, or unwanted sharing with third parties. We align everything with Australia’s Privacy Principles (APPs) for top-tier compliance.
- Enhanced Security for Everyday Use: Our experts configure each phone with a 100+ point checklist, spending 4-7 hours to block leaks, strengthen defences against hacks, and install only trusted apps. Features like quick toggles for your camera, microphone, and location let you control access with a quick tap – no tech degree required.
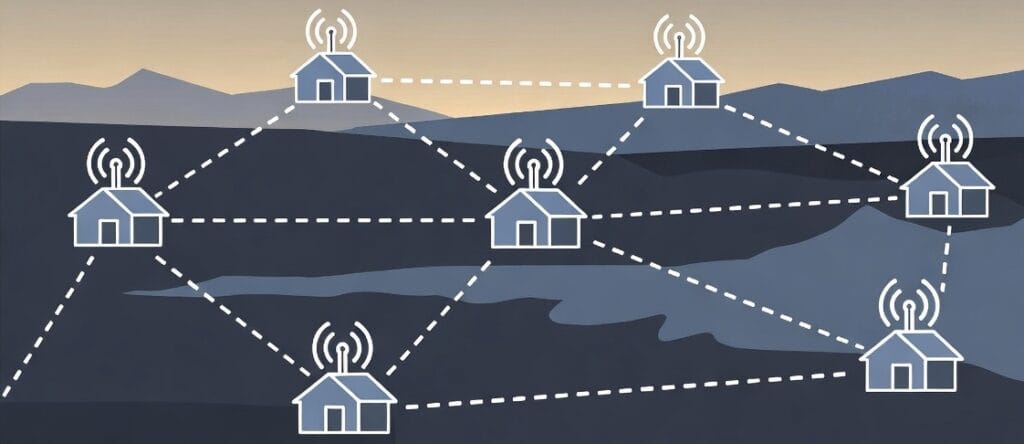
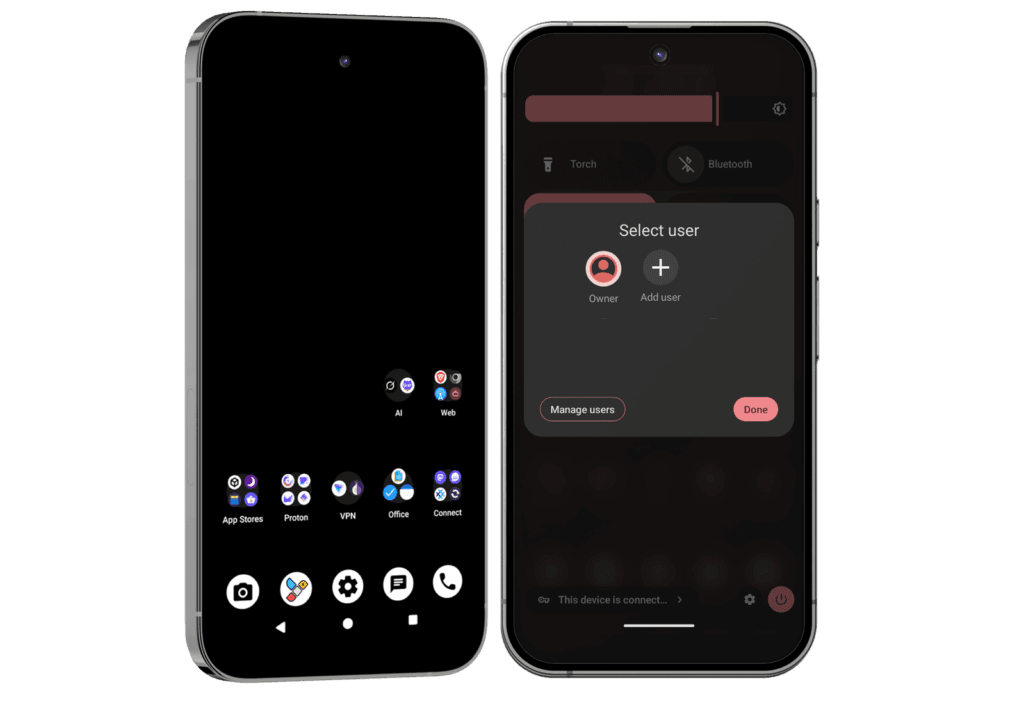
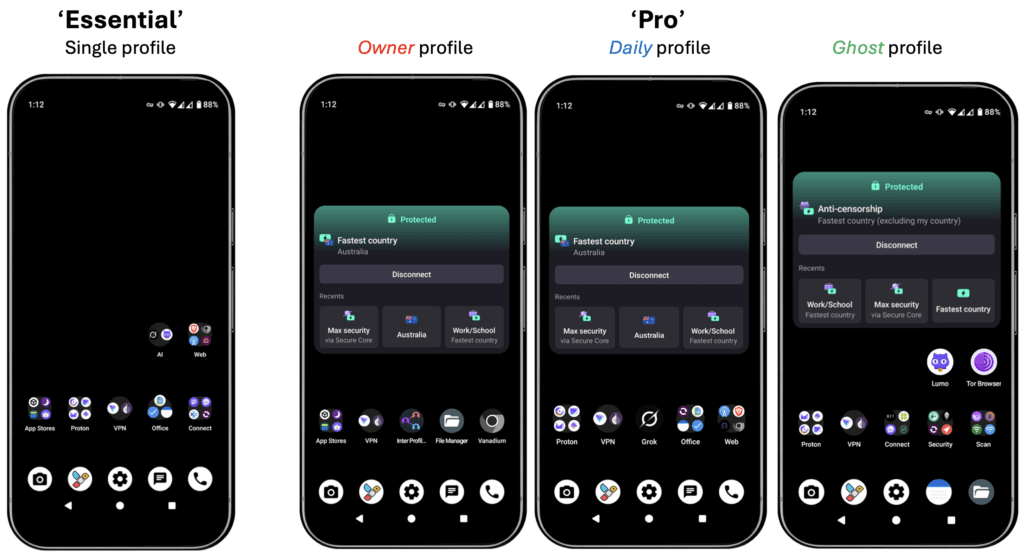
- Seamless Compatibility & Convenience: Works with all major Australian networks (Telstra, Optus, Vodafone, etc). Download apps anonymously without needing an email or personal details. Run apps in isolated “Profiles” or “Private Spaces” – like having multiple secure phones in one.
- Family-Friendly and Versatile: Perfect for parents setting limits on social media or professionals handling confidential work. Use advanced sandboxing (like putting apps in a secure box so they can’t spy on each other) or a duress PIN (a special code that wipes device data instantly in emergencies).
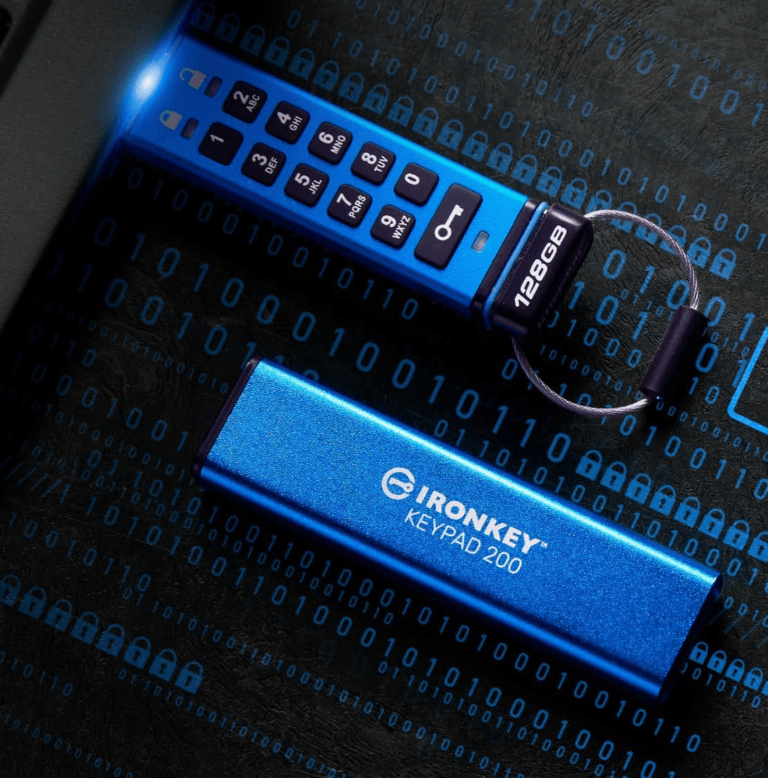
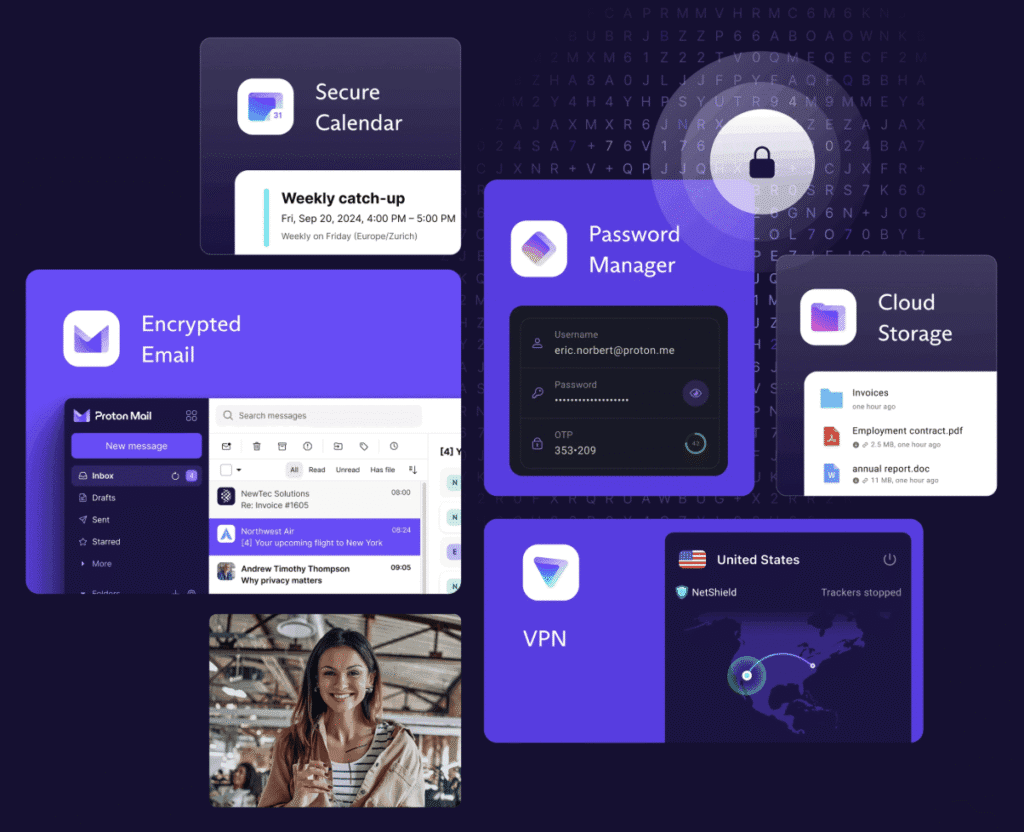
- Eco-Friendly Privacy Ecosystem: Integrate with our partners like Proton for encrypted email, calendar, VPN, and storage – all in one bundle. Enjoy ad-free alternatives for music, videos, podcasts, and maps that minimise your online footprint. Our Pro Bundles even include extras like a premium Faraday bag (blocks signals to prevent tracking), camera covers, and a 1-year Proton Unlimited subscription.
- Ethical and Community-Driven: We’re not just sellers; we’re building digital resilience in our communities. PrivacyPros hosts free workshops across Australia to teach privacy basics. It’s tech with a conscience that gives back.
Common Concerns
We understand some may see “switching” as daunting, but it’s easier than you think.
Here’s how we help with that:
- Will I Lose Features? Not at all! You get full app access, notifications, and even optional sandboxed Google Play (with minimal tracking). Everything runs smoothly on high-end hardware like the Pixel series.
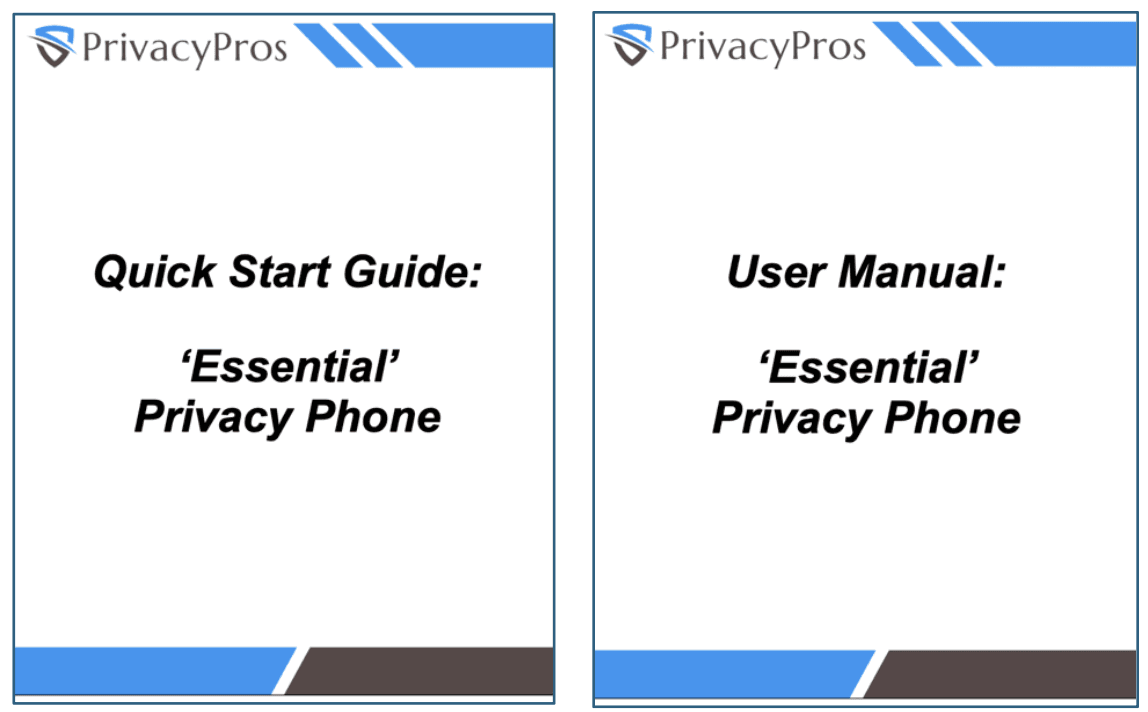
- Is It Hard to Set Up? No DIY headaches here. We handle the complex stuff, and our user-friendly manuals guide you through the rest.
- What About Cost and Reliability? Our phones are new (not refurbished), backed by 2 year warranties, and priced competitively. Avoid risky cheap alternatives.
- How Does It Compare to Regular Phones?
| Feature | Standard Phone (Android/iOS) | Privacy Phone |
| Data Collection | Constant tracking for ads | Zero by default. Your data stays yours |
| Security Controls | Basic permissions | Advanced toggles for sensors, mic, camera, usb port |
| App Installation | Requires accounts | Anonymous downloads, no personal info |
| Compatibility | Network-dependent | Full Aussie network support |
| Privacy Focus | Profit-driven | User-first, with ethical apps + tools |
Privacy is a human right.
You don’t lose your privacy in one big moment. You lose it in thousands of tiny clicks.
Ditch DIY frustrations, generic setups and risky refurbs; switch to Australia’s best de-googled Privacy Phone for privacy, security and anonymity.