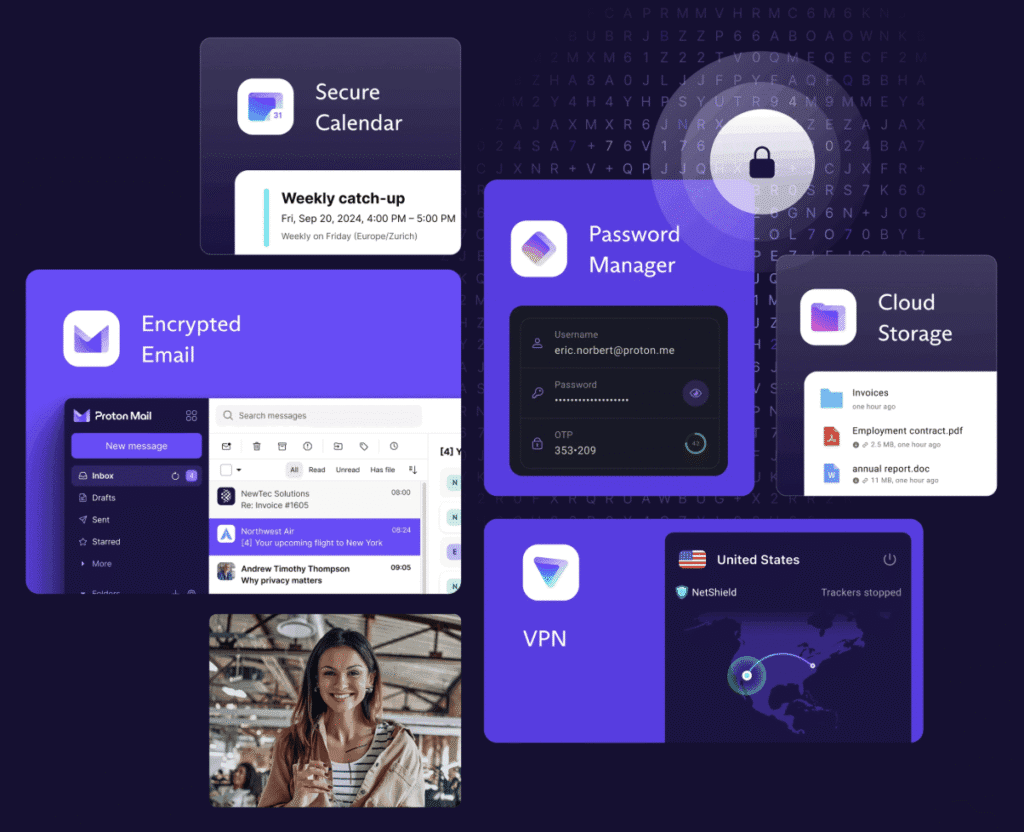
Yes! We have partnered with Proton, and bundle their independently audited, no-logs ecosystem; all pre-installed for seamless Swiss privacy. Proton – trusted by over 100 million users worldwide – is compatible with GrapheneOS’s sandboxing for added isolation.
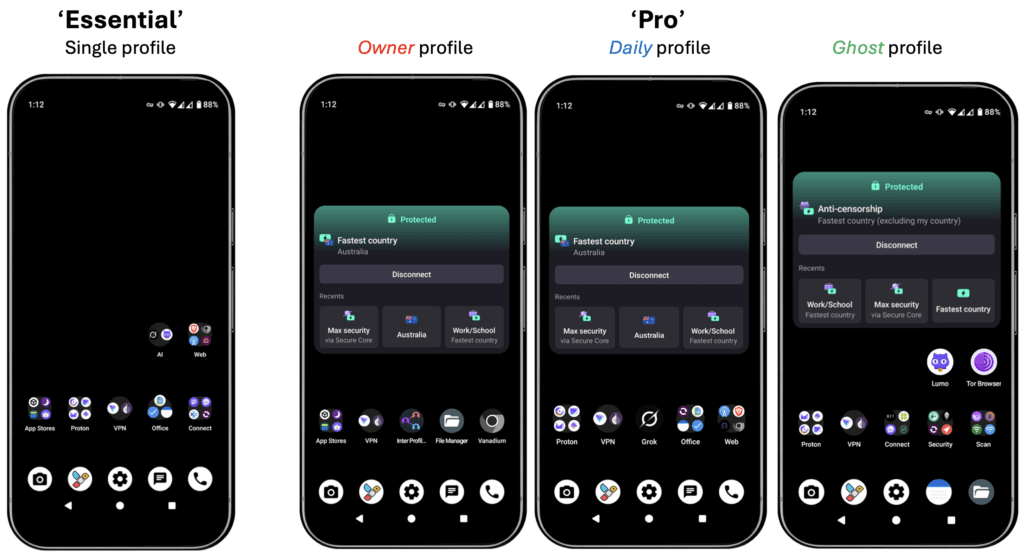
‘Essential’: Proton Free tier delivers core privacy tools, including:
- Encrypted Mail: 1 address, 1GB storage, up to 150 msgs/day.
- VPN: Unlimited data at medium speeds, 1 device, servers in 3 countries (US, Netherlands, Japan), with NetShield for ad/malware blocking.
- Plus: 5 GB Drive, Calendar, Pass (password manager), Wallet; all ad-free, end-to-end encrypted, no logs.
‘Pro Bundle’: Proton Unlimited (1-year included at ~$200 value) provides premium features, including:
- Unlimited Mail: 500 GB storage, unlimited messages, up to 15 addresses/domains/aliases, Proton Scribe AI drafting (on-device or secure no-logs servers).
- High-Speed/advanced VPN: Unlimited data at up to 10 Gbps, 10 devices, servers in 127+ countries (including Australia), Secure Core, Tor integration, custom DNS/split tunnelling, Proton Sentinel (AI+human threat blocking, dark web monitoring), and streaming support.
- Plus: 500GB Drive, advanced Calendar/Pass/Wallet, priority support.
- Full details at https://proton.me/pricing.
Unlock Swiss-grade privacy – shop our de-googled Privacy Phones today!